Is an Uncensored AI Generator Private? What Users Should Check First
Practical checklist to verify privacy of private uncensored AI generators—focus on retraining risk, retention, metadata, payment anonymity, and quick verifications.

Privacy and “uncensored” aren’t the same thing. A platform may let you create bold, NSFW visuals—and still collect prompts, uploads, or analytics that expose you. If you’re evaluating a private uncensored ai generator, start with one critical question: are your uploads and prompts being reused to train models?
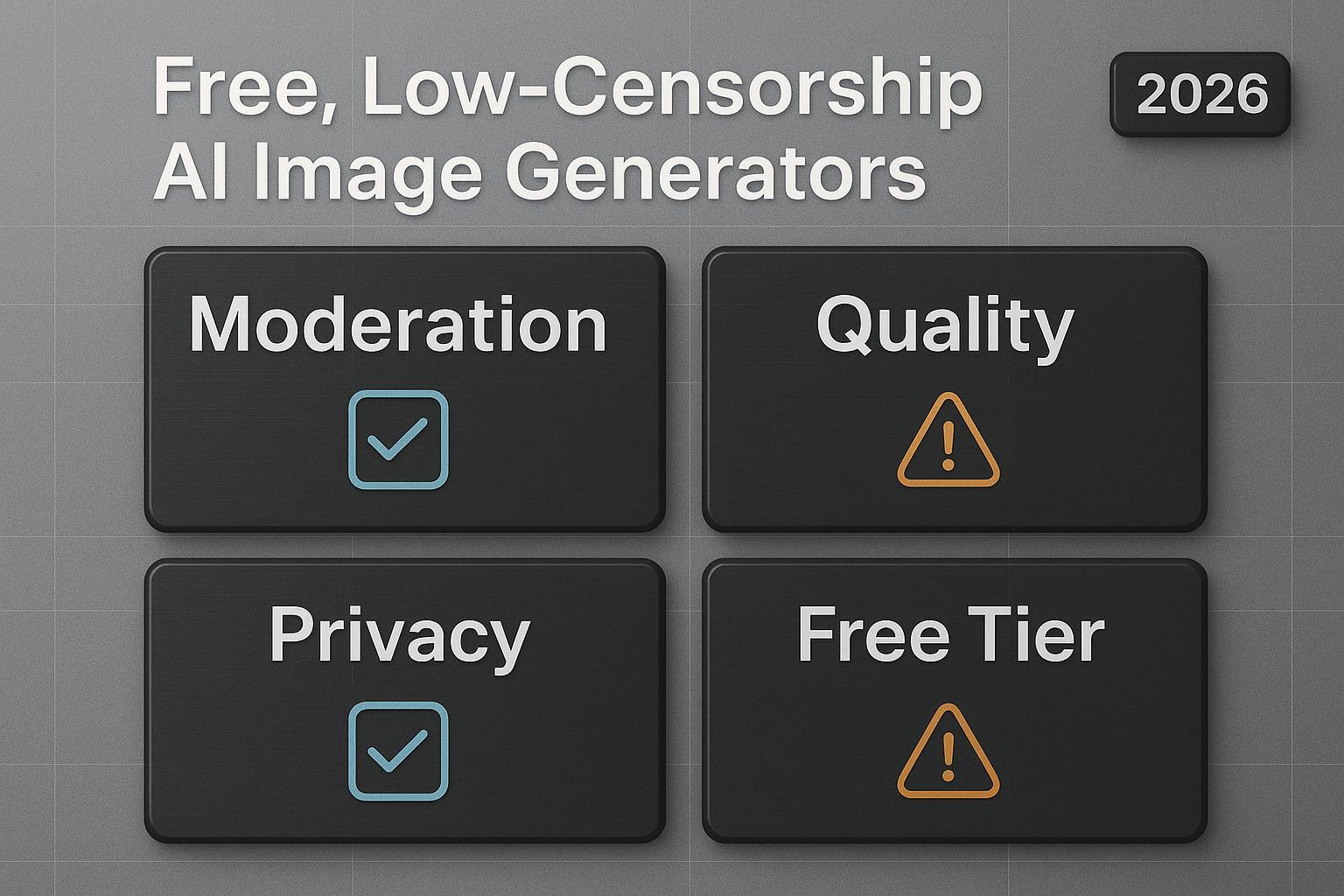
If you’re new to the term, an uncensored AI generator is a creation tool with fewer moderation filters. For a deeper primer on trade‑offs and safe use, see the explainer on what an uncensored AI generator is and isn’t. If you want to evaluate a product experience directly, you can also review the Uncensored AI Generator product page for a sense of how features and privacy claims are presented.
Priority | Check | What you should find | Evidence to capture |
|---|---|---|---|
1 | Training use of uploads/prompts | A clear “we do NOT use your uploads/prompts to train or fine‑tune” or a documented opt‑out | Exact quote + URL/section; support reply if unclear |
2 | Retention & deletion | Concrete windows for prompts/images/logs; deletion/export methods; backup/hold caveats | Quote + URL; screenshot of settings/deletion flow |
3 | Metadata & hosting | EXIF/IPTC behavior; watermarking policy; private or signed image URLs (not public) | ExifTool output; |
The #1 risk: Are your uploads or prompts reused to train models?
This is the privacy lever that matters most for a private uncensored ai generator. If a provider uses your prompts or images to “improve services,” they may funnel sensitive content into training or fine‑tuning datasets. Regulators emphasize that vague language isn’t enough; providers should be specific about training uses and user rights, including opt‑out paths, according to guidance summarized by the IAPP and European authorities in recent years. See the transparency and lawful‑basis discussion in the IAPP’s AI development analysis and the EDPB’s opinions on AI model data use.
How to read policies in 3 minutes
Open the Privacy Policy and Terms of Use. Search for: train, training, improve, model, dataset, fine‑tune, research, service improvement, license, retain.
Look for a plain statement like “we do not use user uploads/prompts to train or fine‑tune our models,” or an opt‑out toggle with scope and effect.
Capture the exact sentence, section heading, and URL. If the language is vague or contradictory between pages, treat it as a red flag and email support for clarification.
Verify with your browser: do inputs leave your device?
Use Chrome DevTools to watch the network during upload/generation. The official docs explain the panels and filters in the Network overview.
Open DevTools → Network. Ensure recording is on. Trigger an upload or click Generate.
If you see large POST/XHR requests with your image or prompt payload going to api/cdn endpoints, your inputs are handled server‑side (and might be retained). If nothing leaves the device, that supports a local‑processing claim.
Retention, logs, and deletion controls for a private uncensored ai generator
Good privacy practice means clear, time‑bound retention windows, deletion flows that actually work, and honest handling of backups and legal holds. European guidance highlights storage limitation and the challenges of effective erasure in AI contexts—organizations should define windows and avoid indefinite retention. See the EDPB’s notes on implementing erasure and retention.
What to do:
Scan policies for retain, retention, deletion, erase, backup, legal hold, logs, telemetry. Note windows for prompts, uploaded images, generated images, and server logs.
Ask support: “What are the retention periods for prompts, uploads, generated images, and logs? Are backups exempt? What is the SLA for deletion requests?” Save the response.
Metadata, watermarking, and traceability
EXIF/IPTC metadata can expose timestamps, software, and other context. Some platforms also add invisible watermarks or Content Credentials for provenance.
Quick checks you can run:
View all embedded metadata with ExifTool:
exiftool image.jpg. Remove it:exiftool -all= image.jpg(creates a backup by default). See the official ExifTool FAQ and docs for options.Understand that invisible watermarks aren’t removed by EXIF/IPTC stripping. The C2PA initiative provides cryptographic provenance; see the C2PA explainer and specification.
Practical example (neutral): Some providers document metadata or watermark behavior on their policy pages. For instance, DeepSpicy maintains a Privacy Policy and a product explainer; review exact wording to see what, if anything, is logged or embedded during creation. Keep expectations tied to what’s written.
Account and payment anonymity
Account requirements can deanonymize you even if creative data is handled well. Check whether email/phone verification or KYC is required and what payment methods are supported.
What to expect:
True anonymity is hard with traditional cards: payment processors and banks create a trail. If a platform supports prepaid cards or privacy‑oriented options, it may reduce traceability, but read billing policies carefully.
If you use a pseudonymous email, don’t forward it to your real identity. Consider how receipts, invoices, and support tickets are handled and stored.
Third‑party trackers and CDN exposure
Analytics, session replay, and public CDNs can leak sensitive information.
Trackers: Use Privacy Badger or similar tools to spot third‑party analytics. The EFF explains why widespread tracking increases exposure and how blocker tools help; see their guidance on fighting back against online tracking.
CDN exposure: If generated images are served from public‑read storage, anyone with the URL can view them. Paste an image URL into an incognito window; if it loads without auth, it’s public. Secure patterns use signed URLs with short expiries; see AWS’s overview of private content with CloudFront.
Standard checklist you can copy (12 items)
Use this when vetting any private uncensored ai generator. Capture quotes, URLs, and screenshots for anything material.
Retraining policy: A sentence explicitly stating uploads/prompts are not used for training/fine‑tuning—or a clear opt‑out path.
Terms vs Privacy consistency: No contradictions between pages about data use.
DevTools evidence: Network tab shows whether prompts/uploads are sent to servers; note domains and endpoints.
Retention windows: Concrete time frames for prompts, uploads, generations, and logs; no “indefinite” catch‑alls.
Deletion path: Self‑service deletion or documented process with SLA; ask about backups and legal holds.
Metadata policy: EXIF/IPTC behavior is documented; you can verify with ExifTool.
Invisible watermarking: Policy states whether outputs carry invisible marks or Content Credentials—and how to disable if offered.
Access control on URLs: Image links are private or signed, not publicly readable in incognito.
Account requirements: Email/phone/KYC expectations are clear; pseudonymous signup is allowed if claimed.
Payment traceability: Supported methods and how billing data is stored; availability of lower‑trace options.
Third‑party services: Analytics/replay SDKs are disclosed; you can identify them in Network requests.
Support responsiveness: Vendor answers policy questions with specifics and links; vague responses are documented as risks.
FAQ
Does local (on‑device) generation guarantee privacy? Not entirely. Local models reduce exposure, but your prompts, previews, or telemetry can still flow to the cloud if the app calls remote APIs for enhancements or analytics. Use DevTools to confirm what actually leaves your machine.
Is stripping EXIF/IPTC enough to stay private? It helps, but invisible watermarks and Content Credentials can persist in pixels even after EXIF/IPTC removal. Decide whether provenance features fit your needs, and test a sample with third‑party viewers.
Does “uncensored” affect legality? Moderation level doesn’t override local laws. Many services still prohibit illegal content and cooperate with lawful requests. Read the Terms and content policy to understand boundaries and how reports are handled.
What if a provider won’t confirm their training policy? Treat it as unresolved risk. Save your inquiry, consider alternatives, or switch to a setup you can verify (e.g., documented non‑training language and local preprocessing you can observe in DevTools).
If you need a broader introduction before diving into this checklist, the concept piece on what an uncensored AI generator covers provides helpful context. When you’re ready, run this checklist before your next creation session.